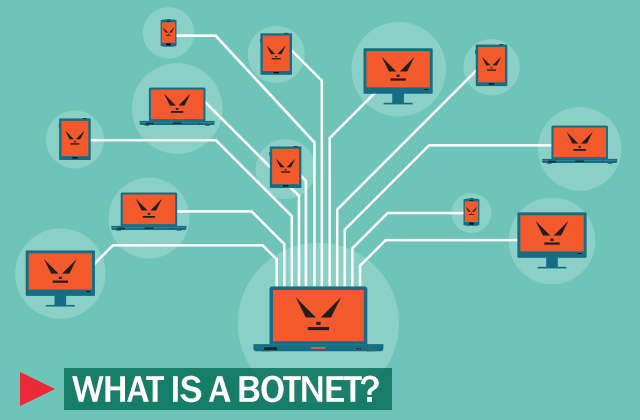
Botnet is the generic name given to any collection of compromised PCs controlled by an attacker remotely — think “virtual robot army.” The individual PCs that are part of a botnet are known as “bots” or “zombies,” and their owners may not even know they’re being used.
Botnets history
Botnets first entered the public consciousness in early 2000, when a Canadian teenager launched a series of distributed denial-of-service (DDoS) attacks against several high-profile websites. The teen, using the handle Mafiaboy, targeted Yahoo, ETrade, Dell, eBay, Amazon, and other sites over the course of several days, flooding the sites with massive amounts of junk traffic until their servers crashed.
Although Mafiaboy (whose real name is Michael Calce), didn’t use a botnet to launch his attacks, security experts warned in the aftermath of the episode that botnets — and the DDoS attacks they’re used for — posed a major threat to the stability and integrity of the Internet. Those experts turned out to be right on the money.
What botnets actually are
Botnets are typically created by a specific attacker or small group of attackers using one piece of malware to infect a large number of machines — although there’s no minimum size for a group of PCs to be called a botnet. The individual PCs in a botnet are generally called “bots” or “zombies.”
Smaller botnets can be in the hundreds or low thousands of infected machines, and larger ones can run into the millions of PCs. Examples of well-known botnets that have emerged in recent years include Conficker, Zeus, Waledac, Mariposa and Kelihos. A botnet is often discussed as a single entity, but the creators of malware such as Zeus will sell their wares to anyone, so at any given time dozens of separate botnets may be using the same malware.
How botnets are made: Methods of infection
There are two main methods through which attackers infect PCs to make them part of a botnet: drive-by downloads and email. Drive-by download infections require a few different steps for the attacker, and they require the attacker to find a popular Web site with an exploitable vulnerability. The attacker then loads his own malicious code on the site and rigs it to exploit a vulnerability in a common browser such as Google Chrome or Internet Explorer. The code will typically then redirect the user’s browser to another site controlled by the attacker where the bot code will be downloaded and installed on the user’s machine.
The email infection vector is much simpler. The attacker sends out a large batch of spam that includes either a file such as a Word document or PDF with malicious code in it, or a link to a site where the malicious code is hosted. In either case, once the attacker’s code is on the user’s machine, that PC is now part of the botnet. The attacker can issue remote commands to the PC, upload data from the machine, download new components and generally do what he wants with it.
What botnets are used for
The traditional and most common use for botnets is in DDoS attacks. These attacks rely on the computing power and bandwidth of hundreds or thousands of PCs to send huge amounts of traffic at a specific Web site in an effort to knock the site offline. There are many different flavors of DDoS attacks, but the goal is the same: preventing the target site from operating.
Attackers used to employ this tactic as a way to knock their rivals’ sites offline, but they then began turning it on Web portals such as Yahoo and MSN, shopping and banking sites and government sites. Groups such as Anonymous, LulzSec and others recently have used DDoS attacks against defense companies, banks and other organizations.
Meanwhile, cybercriminals have taken to using DDoS attacks against banking sites as a way to disguise deeper attacks on those banks. Botnets also are used in a number of other operations. Spammers employ botnets to send out millions of junk email messages from the infected PCs and cybercriminals use them in large-scale credit-card fraud operations.
How to protect from botnets
There are a number of defenses against the DDoS attacks that botnets are used for, but nearly all of them are on the ISP or server level. For users, the defense against becoming part of a botnet is to keep all of the software on their machines patched and up-to-date and to resist clicking on suspicious links. Attackers rely on the gullibility of users to open malicious attachments or click on shady links in order to get their malware onto new PCs. Removing that from the equation makes it far more difficult for attackers to build and use botnets.hat from the equation makes it far more difficult for attackers to build and use botnets.
 botnet
botnet

 Tips
Tips