
XChat: what’s wrong with Elon Musk’s new messaging app?
We break down Elon Musk’s new messaging app, XChat: here’s what we know about its end-to-end encryption, and whether the new service can truly compete with Signal, WhatsApp, and Telegram.

130 articles

We break down Elon Musk’s new messaging app, XChat: here’s what we know about its end-to-end encryption, and whether the new service can truly compete with Signal, WhatsApp, and Telegram.

We break down how cybercriminals are using fake IPTV apps to spread malware, and how you can protect your devices and data during the World Cup.

The new VoidStealer Trojan utilizes a novel method to bypass Chrome’s App-Bound Encryption, allowing it to hijack sessions and steal user data.

We’re breaking down why developers have moved into the crosshairs, the specific tactics attackers are using, and how to reduce the risks of company infrastructure being compromised.

The emergence of DarkSword and Coruna — new malware targeting iOS — shows exactly how government intelligence tools are being repurposed as weapons for cybercriminals. We break down how these attacks work, why they’re so dangerous, and what you can do to not get infected.

Smart sex toys and their companion apps collect and process some extremely personal data. We break down the risks involved, and ways to protect your privacy.

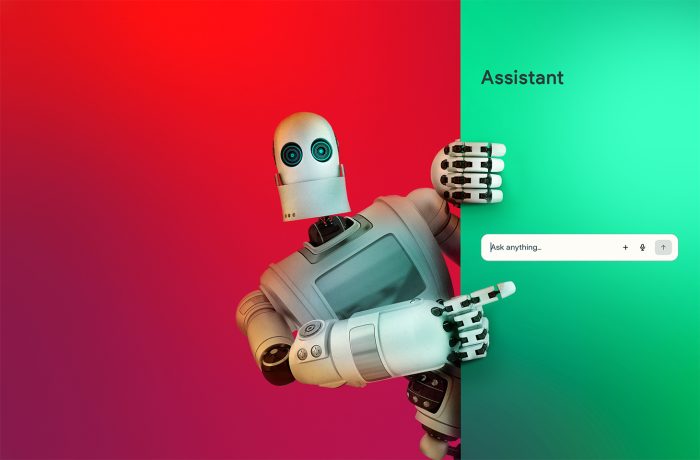
Researcher Niels Provos’ prototype IronCurtain architecture: a system designed to restrict the actions of AI agents through isolation and security policies.

Intellexa’s Predator spyware can hide camera and microphone usage indicators on iOS devices. Here’s a look at how it pulls it off.
A browser-in-the-browser attack, theoretically described in 2022, has been adopted in real-world phishing. We break down how it works, and how to spot a fake authentication window.

Children’s AI toys have been caught discussing drugs and sex with kids. We break down the results of a study that reveals exactly how these smart (too smart!) toys are blowing up past boundaries.

Researchers have discovered that styling prompts as poetry can significantly undermine the effectiveness of language models’ safety guardrails.
Generative AI has taken sextortion techniques to a whole new level — now, any social media user can become a victim. How can you protect yourself and your loved ones?

From karaoke rooms to gynecology clinics — these are just some of the tens of thousands of locations where compromised IP cameras were discovered in South Korea. Here’s how to avoid unwittingly starring in steamy videos you didn’t authorize.

How automation turns legitimate tools into a channel for malware delivery.

How researchers hacked DeckMate 2 card shufflers, and how the mafia exploited those very vulnerabilities to cheat at poker.
How malicious extensions can spoof AI sidebars in the Comet and Atlas browsers, intercept user queries, and manipulate model responses.
Malicious actors have started utilizing a new variation of the ClickFix technique — named “FileFix”. We explain how it works, and how to defend your company against it.

Official gaming websites and platforms may seem safe, but even there gamers occasionally encounter malware. We break down infection cases involving Endgame Gear, Steam, and Minecraft.

WordPress sites are increasingly becoming targets of attacks exploiting vulnerabilities in plugins and themes. In this post, we examine recent cases and share protection tips.

Deepfake videos, fraudulent Instagram and Facebook accounts, private WhatsApp chats: how Mark Zuckerberg’s social media platforms have become a primary tool for investment scammers.

How the research tool Defendnot disables Microsoft Defender by registering a fake antivirus, and why you shouldn’t always trust what your operating system says.