In this modern, global economy, more workers are doing their jobs remotely. There's no reason to waste money on excessive overhead. Big offices filled with desks aren't necessary when you can have video conference calls and share files with a click. Even retail businesses and the food industry have recognized that POS systems can operate more efficiently over the Internet. Times have changed.
Today, many successful businesses have what are known as endpoint devices as parts of their online networks. These devices make systems work more smoothly by allowing employees and vendors on a variety of levels to work with geographic independence. They can get their jobs done faster while keeping data organized and accessible.
Of course, sometimes it's too accessible. The concern business owners face — regardless of company size — is cybersecurity within such increasingly complex networks. It's important to educate yourself about the potential threats that come with endpoint devices and what you can do to protect your company's assets.
What Is an Endpoint Device?
Years ago, companies typically had a few clunky desktop computers for doing business. Look around, and you'll recognize that your company probably is nothing like that anymore. You're likely operating with a large number of endpoint devices. These are Internet-capable machines that function with computer hardware on a network.
Examples of endpoint devices include:
- Desktop computers
- Laptops
- Tablets
- Smartphones
- Printers
- Point-of-sale (POS) terminals.
If you have a machine connected to your network, it's an endpoint device that's part of the efficient way you've set up your company's technology.
One of the unique challenges that endpoint devices present is that some can also access many different networks — and may do so regularly. This opens them up to a multitude of opportunities for hackers on other networks to steal information. Consider smartphones and tablets. Employees can take them out of the office and connect to unsecured Wi-Fi networks at the nearby coffee shop or a hotel across the country. This exposure increases security vulnerabilities when it comes to hackers retrieving sensitive company data that's stored or accessed on company devices.
Cyberattacks Made for Mobile
Creating an inventory of your endpoint devices is a crucial first step. It gives you a big-picture look at the potential for cyberattacks that steal valuable financial and private data your business needs. The reality is that an endpoint device is now the first place hackers check for system or network vulnerabilities.
Consider this: what information does your office printer have access to? All your files so you can print anything out with a touch of the button? Also, all those smartphones your employees use contain very sensitive data. Often, IT professionals and business owners don't realize the risk they create by sharing information.
Understanding Vulnerabilities
Why are endpoint devices like voiceover internet protocol (VoIP) phones, scanners and smart meters vulnerable? Put yourself in the shoes of a hacker looking for easy access to sensitive information. The more common endpoint devices become, the easier targets they become for hackers.
It's part of the reason why Androids are more at risk than iPhones — there are simply more of them. So, the more companies connect smartphones, laptops and other endpoint devices to their networks, the more likely hackers are to search for weaknesses there. If you don't have a cybersecurity plan that includes endpoint-device protection, hackers will find a weakness.
Make a Plan for Protection
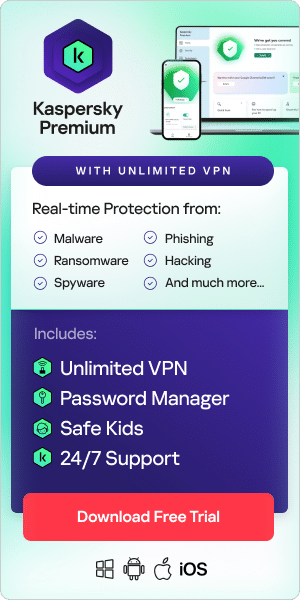
A cybersecurity plan needs to be comprehensive for your entire business operation to be successful. An endpoint security-management plan helps you craft a policy that protects your business at every end. Take the vulnerabilities into consideration: are your company's mobile devices operating under a virtual private network? Do you have a method in place that automatically updates your protection when the latest threat intelligence is released?
Planning ahead — well before any security threats impact your data — brings peace of mind to all levels of your business.
Related articles and links:
What is Cybercrime: Risks and Prevention?
Android vs. iOS – Which is Safer?
Related Products:
Kaspersky Small to Medium Business Security