While there are numerous cybersecurity threats to beware of, spam and phishing are two of the most common and therefore, the two threats users are most likely to encounter. While they can be very similar, there are some subtle differences. The most important thing to remember, though, is that while all phishing emails are scams, not all scam emails are phishing attacks.
Learning the difference between phishing and spam can be helpful in keeping users safe online. But this can result in a host of questions, such as “Is spam a security threat?” and “What are examples of spam and phishing?”
What is the Difference Between Phishing and Spam?
Although they can seem very similar, there are actually subtle differences between spam and phishing. While both involve the sending and receiving of unsolicited emails, the most common spam emails are simply a nuisance. Phishing attacks are more nefarious and present a significant cybersecurity threat to recipients.
When trying to understand the difference between phishing and spam, there is one main thing to remember. Phishing emails use numerous techniques—including social engineering—to lure targets into disclosing sensitive information or personal data. Some signs of a phishing email to be aware of include misspelled words, email addresses that do not conform to an organizational norm, direct requests for personal information, or emotional language.
Usually, a phishing email will impersonate a legitimate organization—banks and ecommerce sites are common—and create a sense of urgency to trick the target into clicking a link or otherwise providing information such as login credentials or credit card details. The attacker can then use these details to perpetrate other crimes, such as financial fraud. In some cases, the email may have a compromised attachment or link that installs malware on the recipient’s device.
There are several different types of phishing, including:
- Deceptive Phishing: This is the most common type of cyberattack and involves the attacker impersonating a legitimate organization in the email.
- Spear Phishing: These attacks target specific individuals or organizations and are more likely to use social engineering techniques to create a sense of legitimacy.
- Whaling: Another very targeted type of phishing attack, these target high-profile individuals, such as company CEOs.
- Vishing: Instead of using email, these phishing attacks are executed through phone calls and usually involve the attacker pretending to represent a legitimate organization to steal personal details.
- Smishing: While similar to vishing, these attacks are carried out by text message instead of voice call but still attempt to steal sensitive information.
Wondering exactly what are spam emails? These are essentially the digital version of physical junk mail. Spam is an unsolicited email intending to sell products or services that is sent in bulk, usually to thousands of individuals at a time. The most common spam emails might include newsletters, solicitations for donations, coupons, and chain forwards. Spam can be annoying for the recipient; they are generally quite innocuous—they do not expressly represent a threat. Recipients can use spam filters and opt-out links to lessen how many spam emails they receive. However, some spam emails also attempt to steal a user’s personal information, which is why they are easily confused with phishing emails.
How to Recognize Spam and Phishing
In many cases, it is easy to tell the difference between phishing and spam emails. However, attackers are becoming increasingly sophisticated, and it can be challenging now to identify exactly whether the email is indeed a cyberattack or is more innocuous. For this reason, it is essential that users learn to recognize examples of spam and phishing.
Phishing emails usually have attributes that make them identifiable, including:
- Purporting to come from an organization, such as a bank or an ecommerce site.
- Email addresses that are slight deviations from a company’s official email domains.
- A more formal tone of voice.
- Urgent, threatening, or emotional language that is designed to make the recipient act immediately.
- A link to a malicious site that the recipient must click on to log into their account or provide the requested information, or a malicious attachment that must be downloaded.
- Subtle misspellings or grammatical mistakes.
Phishing emails employ numerous tactics that might seem innocuous at first glance, such as:
- Saying an account has been temporarily suspended due to suspicious activity and the user must click a link to log into the account and restore it.
- Claiming that there is a problem with billing or payment information and that the recipient must log into their account through the attached link to update these.
- Attaching a fake invoice that will install malware on the recipient’s device when opened.
- Saying that the target has won a prize and must provide personal information to receive it.
- Telling the recipient that they are eligible for a government refund and must provide their social security number to receive it.
Conversely, spamming examples tend to be more casual in nature, use random sender addresses and domains, and usually contain promotional content. Spamming email examples often include generic greetings and some kind of advertising or marketing material, and do not actively try to force the recipient to take action.
Examples of Spam and Phishing
So, what do these types of cyberattacks look like in practice? Below are some of the most common examples of spam and phishing emails to look out for.
Spam emails:
- Fake bank transaction verifications
- Fraudulent account login verifications
- Unexpected game invites
- Malware spam phishing emails
Phishing emails:
- Demands to log in to retain account
- Request to verify billing or payment information
- Prompt to change passwords
- Invites for government programs
- Unexpected gift, payout, or prize
- Fake invoices
- Email account upgrade
How to Protect Yourself from Spam and Phishing Attacks
While the prevalence of spam and phishing attacks makes them largely unavoidable, it is possible for users to minimize the chances of falling victim to these cyberattacks. Here are some useful tips and best practices that can reduce the amount of spam emails and help users stay alert to phishing attacks:
- Set up multiple email addresses: Use one email address only for personal correspondence and never publish this publicly, and a second address for online purposes such as social media accounts, mailing lists, and other internet services.
- Never respond to any spam: Most spammers verify email receipts and log responses, so users who respond are more likely to receive more spam.
- Think before you click unsubscribe: Spammers sometimes send fake unsubscribe emails to attempt to collect active email addresses—by clicking the unsubscribe link in one of these emails, users may increase the amount of spam they receive.
- Keep browsers (and all software) updated: Ensure that web browsers, applications, and software are always kept up to date and running the latest security patches.
- Activate spam filters: Use email providers that include spam filtering as standard, and use an antivirus and internet security solution that also includes advanced anti-spam features.
- Understand the most common attributes of spam or phishing emails: Treat emails suspiciously and look for signs such as misspellings and grammatical mistakes or an unusual sense of urgency—also be on the alert for unexpected emails.
- Never provide personal information over email: Attackers often impersonate legitimate entities—such as banks—and ask the user to log into accounts (through a fraudulent website) or provide credit card details by email. Remember that real organizations will never ask for information in this way.
- Avoid clicking links or opening attachments in suspicious emails: This is often how hackers attempt to steal sensitive information or distribute malware.
- Remember password hygiene: Create complex passwords for each online account and change these regularly—use a password manager to keep track of these.
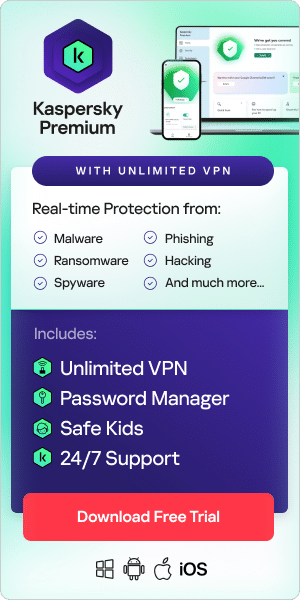
- Use security software: These can help detect phishing and spam attacks before they become a problem—just ensure that the software is always kept up to date.
- Enable multifactor or biometric authentication: Whether this involves an additional passcode or one-time password sent to a phone, or facial recognition, this adds an additional layer of security.
- Regularly back-up data: Whether the data is backed up to an external hard-drive or to the cloud, this ensures that the data is recoverable in case of an attack.
- Report the email: Reporting spam or phishing emails is especially useful in a corporate environment—reporting the emails to the IT department can ensure that these threats are eliminated quickly.
- Turn off email images: Some spam attacks use embedded images that track whether the email is opened—this tells the spammer that the email address is active and can result in more spam.
In conclusion, understanding the distinctions between spam and phishing is crucial for users navigating the digital landscape. While spam inundates inboxes with unwanted content, phishing poses a more insidious threat by employing deceptive tactics to extract sensitive information. Recognizing the hallmarks of phishing, such as urgent language and fraudulent impersonations, empowers users to stay vigilant. As cyber threats evolve in sophistication, users must enhance their ability to differentiate between benign and malicious emails. By adopting proactive measures, such as utilizing spam filters, maintaining updated software, and practicing password hygiene, individuals can fortify their defenses against these prevalent cyber threats. Staying informed about the common attributes of spam and phishing, exercising caution when interacting with emails, and promptly reporting suspicious activity are integral components of a comprehensive cybersecurity strategy. In a digital landscape fraught with challenges, these practices contribute to a safer online experience, minimizing the risks associated with spam and phishing attacks.
Related Articles and Links:
Related Products and Services: