Let’s say someone wants to post their holiday videos to show friends. Instead of paying through the nose for a video editor, they search for “download Adobe Premiere free” or something to that effect. One of the first links takes them to a seemingly innocuous site with decent design, user reviews, and even a feedback form.
At first, everything seems fine. The software downloads, installs, and launches without any trouble — but also without requiring a key or activation code. Our protagonist seems to have lucked out. But then he or she notices that the computer is slower than usual. Games that used to load up without a problem are now taking ages or even crashing. Another surprise comes the following month: The electricity bill is quite a bit higher than usual.
What’s going on?
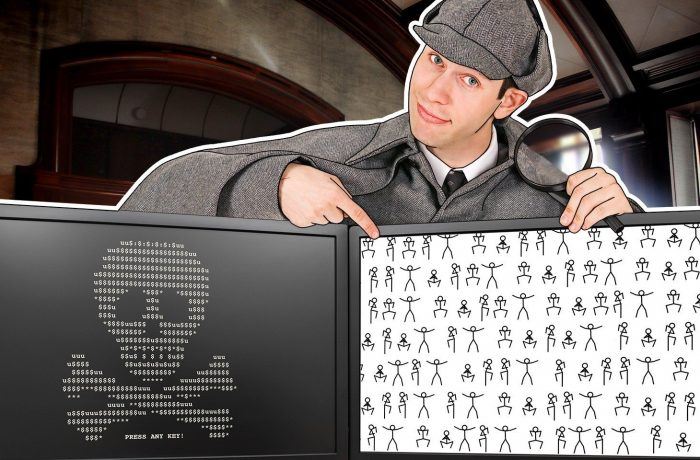
Free software and parasitic miners to boot
We’ve already warned about the dangers of downloading “free” versions of non-freeware programs. It’s a false economy with potentially nasty consequences. Among the latter, recent years have seen a spike in the number of attempts to earn money at the expense of freebie lovers through embedding miners in such programs (for info about what miners are, see here and here).
That’s exactly what happened to our hero: The pirated video editor installed a special version of the NiceHash miner, configured to mine straight into the pirates’ cryptowallets.
The naive penny-pincher is earning cash for cybercriminals without even realizing it. To keep the miner out of mind, the intruders keep it out of sight. The program window is collapsed and not displayed among the running applications. The only visible evidence is a tiny icon at the bottom of the screen, next to the ones for volume control and clock.
Games and other resource-intensive programs start to slow down because the miner makes full use of computer resources, including the video card, to mine cryptocurrency. And our freebie lover’s electricity bill shoots up because mining is an extremely energy-intensive process; hence the computer consumes more power than usual.
However, people trying to avoid paying for premium software are not the only ones at risk of picking up an unwanted miner. Genuine freeware can include unwanted extras, too. You should download such apps only from the developer’s official site. Recently, our experts discovered a number of sites distributing free and pirated applications bundled with a miner. Among them were OpenOffice, TeamSpeak, Adobe Premiere Pro, ABBYY Fine Reader, CorelDraw, Microsoft Outlook, Microsoft PowerPoint, Microsoft Office Picture Manager, and XPadder.
How to protect yourself
To avoid sharing your computer’s resources with cybercrooks, follow these simple rules:
- Download all programs, including legitimately free ones, only from official developer sites or official app stores.
- Install a reliable security solution — for example, Kaspersky Plus.
- Enable riskware detection in your security solution.
Mining programs as such are legal for people who want to install them on their computer to mine cryptocurrency. Therefore, antivirus utilities do not always block miners, in particular if they cannot accurately determine whether the program was installed by the user or a cybercriminal. Security solutions identify such programs as riskware or not-a-virus — legitimate software that can be exploited by intruders.
For details about how to enable this function in Kaspersky Internet Security, see here.
 threats
threats