Sometimes we have no other option than to leave our things unattended. Imagine the situation: you are alone at the beach on a hot summer day and cannot resist the temptation to jump in the water. Or maybe your distracted by something entirely different from your bag and pockets. So what do you do when you notice that your phone is missing?
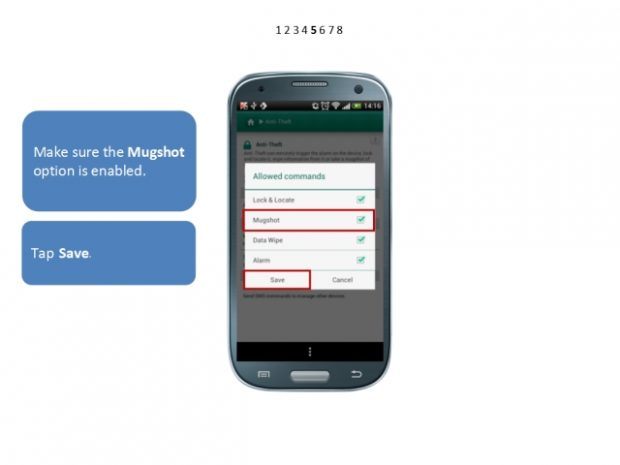
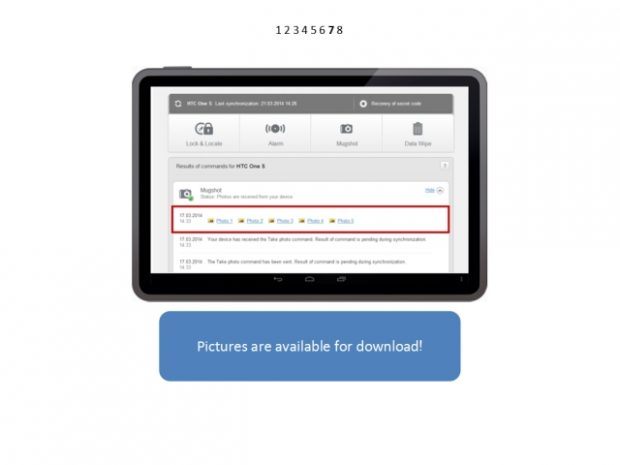
Today we are going to explain how Kaspersky Internet Security for Android can help you find a thief.
 Android
Android