
How the adversary-in-the-middle technique is used in spearphishing attacks
Cybercriminals are using AitM techniques to compromise accounts of company executives. How do they do this, and how to protect against it?
509 articles

Cybercriminals are using AitM techniques to compromise accounts of company executives. How do they do this, and how to protect against it?

Although Microsoft has radically revised the rollout plan for its controversial Recall feature, cybersecurity teams can’t afford to ignore the issue of “AI onlookers.

The story of how CrowdStrike released an update on a Friday and brought down thousands, tens of thousands, or maybe even hundreds of thousands of computers around the world.

A zero-day vulnerability actively exploited by attackers has been discovered in Internet Explorer — the browser that Microsoft supposedly laid to rest over a year ago.

Medium-sized businesses increasingly find themselves on the receiving end of targeted attacks. What tools does one need when basic security proves inadequate?

Someone is targeting security experts using an archive that allegedly contains an exploit for the regreSSHion vulnerability.

The JavaScript CDN service Polyfill.io has started spreading malicious code. Remove the service’s script from your website.

Developers’ accounts are being hijacked using fake job offers sent from a legitimate GitHub address.

Based on our analysis of ZKTeco vulnerabilities, we dissect the risks associated with biometric authentication.

Our experts have discovered ransomware they’ve dubbed “ShrinkLocker”, which encrypts infected computers’ drives using BitLocker — a utility built into Windows.

Cybercriminals are using genuine Facebook infrastructure to send phishing emails threatening to block accounts.

Threat actors are targeting hotel staff with malicious and phishing e-mails.

We’ve released a free application that allows you to scan Linux systems for known cyberthreats.

Today we discuss which services and applications should be patched first, and what attackers are focusing on.

dormakaba Saflok locks — used on around three million doors across 13,000 hotels — are vulnerable to an attack that involves forging electronic keycards.

Cybercriminals prey on corporate credentials by sending phishing links through Dropbox after priming the victim.
Kaspersky ICS-CERT experts have discovered several critical vulnerabilities in Telit Cinterion M2M modems, which are used in millions of devices.
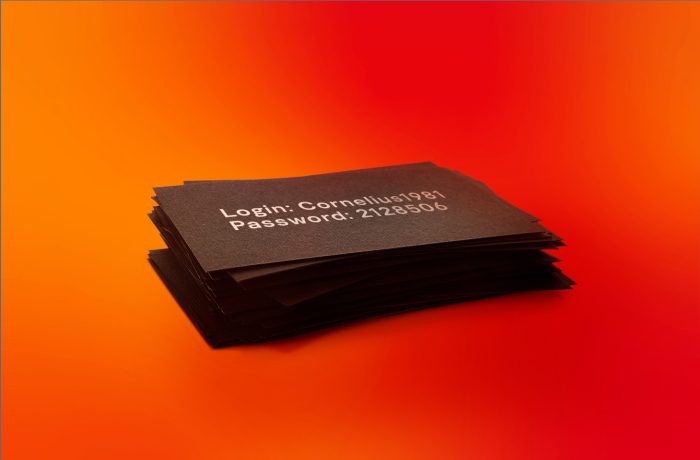
A credential stuffing attack is one of the most effective ways to take control of accounts. Here’s how it works and what you should do to protect your company.

Dropbox has shared a report on a data breach in the Dropbox Sign e-signature service. What does this mean for users, and what should they do?

Expanding Global Transparency Initiative by opening Istanbul Transparency Center and launching a Transparency Lab together with Boğaziçi University