
2018 Soccer World Cup safety tips
How to avoid getting phished or otherwise duped on the eve of the 2018 World Cup in Russia.
3148 articles

How to avoid getting phished or otherwise duped on the eve of the 2018 World Cup in Russia.

How scammers are exploiting the GDPR fuss to extract personal data.

Implementing effective cybersecurity technologies does not equal GDPR compliance, but it is among the cornerstones on which this compliance is built.
Advertising in voice assistants is coming soon. We examine how it will use personal data and what you can do about it.

What is the cost of an incident that affects corporate data? Which threats are the most expensive? Learn that and more from our latest research.

Jeff and Dave discuss a fake Fortnite app, China visiting the dark side of the moon, Facebook breakup, Teensafe, and more.

Here’s how scammers try to phish for verification codes — and what may happen if you send them one.

A look at how payment information is protected on smartphones that support contactless payments.
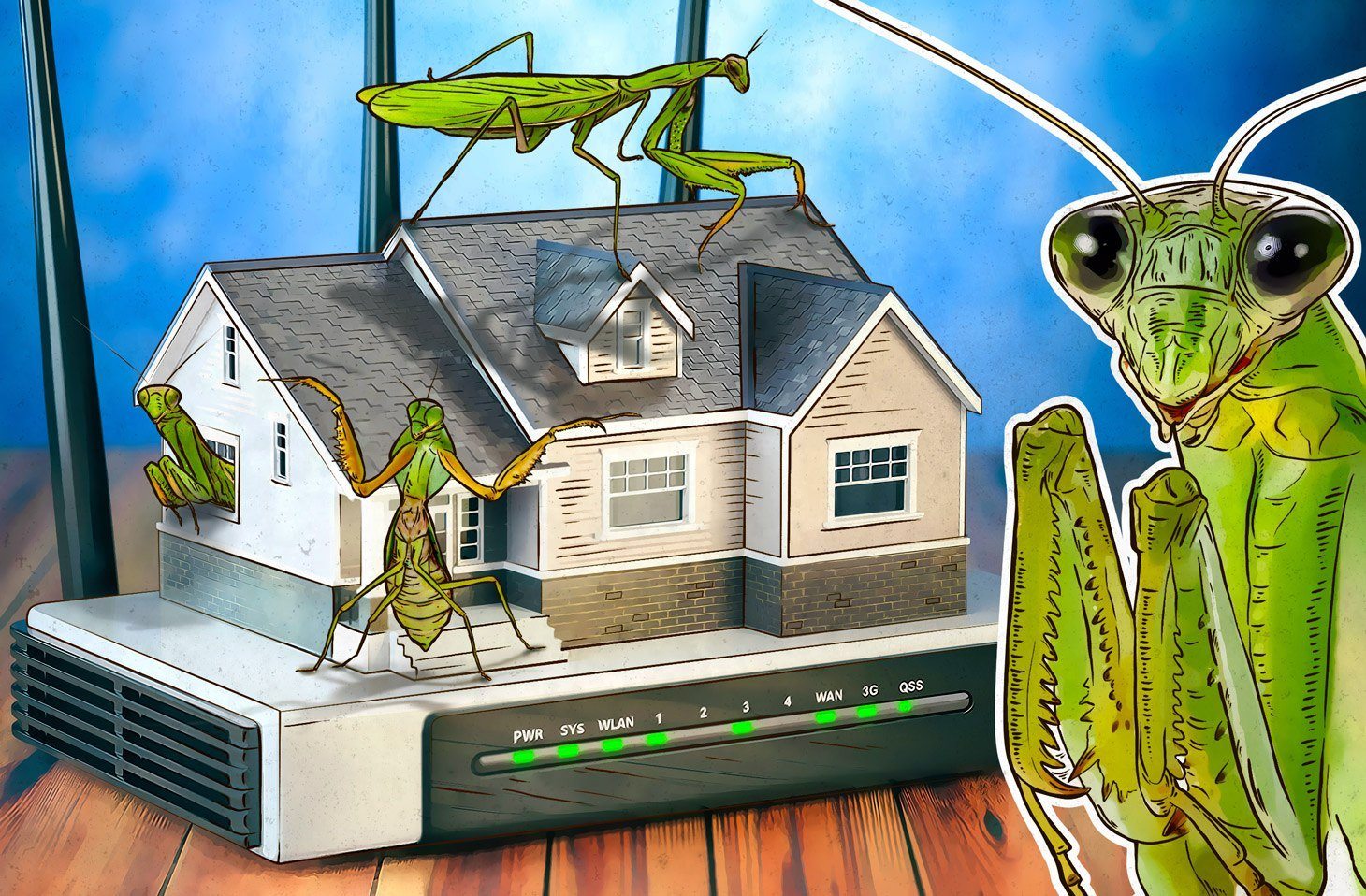
Originally targeting users from Japan, Korea, and China, Roaming Mantis is quickly spreading worldwide, infecting smartphones through hacked wi-fi routers.

In this week’s podcast, Jeff and Dave riff on the Chili’s data breach, Facebook’s internal reviews, police falling victim to ransomware, and more.

Our first Transparency Center, as well as “software assembly line” and storage of Kaspersky Security Network data, will be located in Switzerland.

Do you follow the news? The news may also be following you. ZooPark spyware targets those partial to politics.

Jeff and Ahmed discuss privacy online, the latest on Cambridge Analytica, and more.

How can we get prepared for the decryption capabilities of upcoming quantum computers?

How Twitter’s “not-a-leak” made me realize that remembering passwords no longer works.
If your Kaspersky product tells you something about an “Invalid key file” or ”Integrity violation,” here’s what to do.

This new version of SynAck ransomware uses sophisticated evasion techniques.

How Kaspersky Endpoint Security for Business counters the latest threats

Ten mistakes that led to the destruction of the Death Star.

Jeff and Dave discuss a Facebook dating app, Twitter selling data to Cambridge Analytica, and more.