
Don’t help pickpockets — set up a PIN to unlock your phone
No PIN on your phone? Pickpockets will thank you for that.
634 articles

No PIN on your phone? Pickpockets will thank you for that.

As we predicted at the end of 2017, malicious cryptomining is booming in 2018, up by 44%.

Targeted attacks are dangerous, but that doesn’t mean you should forget about threats that are more common.

In part one of our mobile malware series, we cover infectious Android malware — adware, subscribers, and flooders — and how mobile viruses can damage your smartphone or tablet…

How tools designed to study and protect rare species can turn from gamekeeper to poacher.

Did you see that new fully loaded Android smartphone, the one that looks too good for the price? Well, it may include some unwanted extras.

We investigate intercepting smartwatch motion-sensor data to monitor people and steal information.

How to avoid getting phished or otherwise duped on the eve of the 2018 World Cup in Russia.

How scammers are exploiting the GDPR fuss to extract personal data.

Here’s how scammers try to phish for verification codes — and what may happen if you send them one.
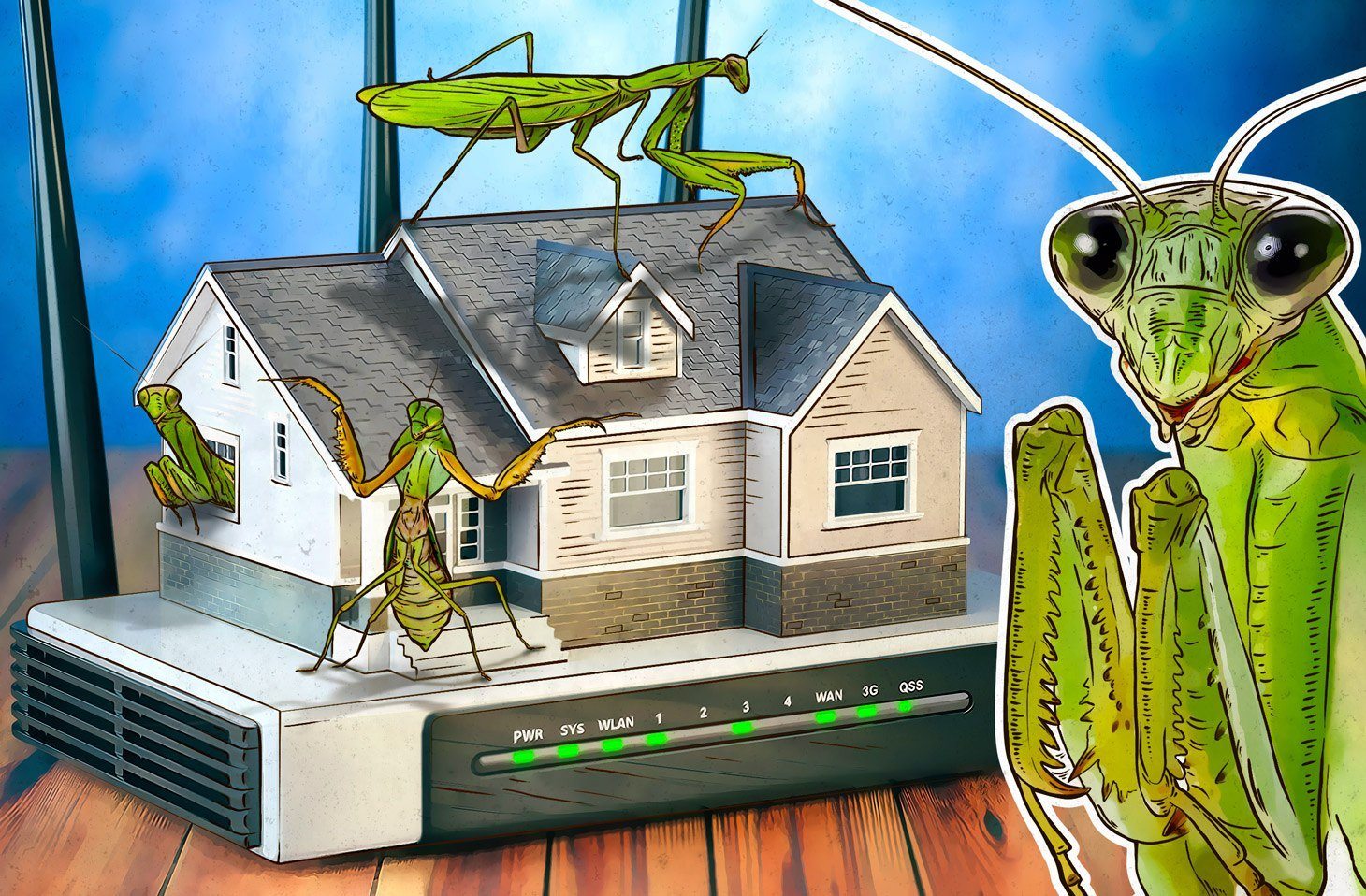
Originally targeting users from Japan, Korea, and China, Roaming Mantis is quickly spreading worldwide, infecting smartphones through hacked wi-fi routers.

Do you follow the news? The news may also be following you. ZooPark spyware targets those partial to politics.

This new version of SynAck ransomware uses sophisticated evasion techniques.

Fake airline giveaways won’t win you a ticket, but they might steal your data.

Even very popular apps display ads using third-party code, which can transmit personal data unencrypted.

Malefactors are massively exploiting a vulnerability in Cisco switches, taking down entire segments of the Web.

Hidden miners detected in soccer and VPN apps on Google Play — steer clear!

Most computer infections come from visiting porn sites, or so some people say. Are they right?